cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.
Blockchain Tracing: A Key Tool in Crypto Asset Recovery
The cryptocurrency ecosystem has expanded rapidly, with billions of dollars in digital assets now in circulation across thousands of blockchains. However, this growth has been accompanied by significant risks, including hacks, scams, phishing attacks, and user errors such as lost private keys or forgotten seed phrases. In 2025, reported losses from crypto-related incidents exceeded several billion dollars, highlighting the persistent vulnerability of digital assets. Unlike traditional banking systems with reversible transactions and centralized oversight, blockchain's decentralized and immutable nature makes recovery difficult once funds are transferred. As a result, blockchain tracing has emerged as an essential method for identifying fund flows, attributing activity, and supporting recovery efforts in actionable cases.
By Garry Oneal2 months ago in 01
The Complete Guide to Recovering Your Snapchat Password (Legitimate Methods & Protection Tips). AI-Generated.
Losing access to your Snapchat account can be frustrating and concerning. Whether you've forgotten your password or suspect unauthorized access, this comprehensive guide provides legitimate recovery methods, essential protection strategies, and answers to frequently asked questions. It's crucial to emphasize that hacking into someone else's Snapchat account is illegal and unethical. This article focuses exclusively on legitimate account recovery for your own account and protective measures.
By Alexander Hoffmann2 months ago in 01
How to Recover Your Instagram Password: Ethical Methods and Security Guide. AI-Generated.
Losing access to your Instagram account is frustrating. Whether you've forgotten your password or suspect unauthorized access, this guide provides the most effective recovery methods currently available. We'll explore legitimate recovery options, review password security tools, and offer essential protection strategies. Important note: This article covers password recovery for your own account only. Unauthorized access to others' accounts violates Instagram's terms and may be illegal.
By Alexander Hoffmann2 months ago in 01
The Complete Guide to Wi-Fi Hacking: How Networks Are Compromised and How to Protect Yours. AI-Generated.
The Invisible Threat to Your Wireless Network In our hyper-connected world, Wi-Fi has become as essential as electricity. From smart homes to remote work, we depend on wireless networks for virtually everything. Yet, this convenience comes with significant risks. Wi-Fi hacking represents one of the most pervasive and potentially damaging cyber threats facing individuals and organizations today. Understanding how these attacks work isn't just technical knowledge—it's a necessary layer of digital self-defense in our increasingly wireless world.
By Alexander Hoffmann2 months ago in 01
AI Race in 2026
By 2026, the global race in Artificial Intelligence (AI) has moved far beyond simple innovation. It has become a strategic competition that shapes economies, national security, education, healthcare, and daily life. Governments, technology giants, startups, and research institutions are all competing to lead in AI development. This race is not only about creating smarter machines, but also about controlling data, setting global standards, and defining how humans and machines will coexist in the future.
By shaoor afridi2 months ago in 01
The Ultimate Guide to Regaining Access to Your Instagram Account. AI-Generated.
Lost access to your Instagram account? Our comprehensive guide covers official recovery methods, security protocols, preventive measures, and answers to all your questions about restoring your Instagram presence.
By Alexander Hoffmann2 months ago in 01
Design Principles Behind High-Trust Digital Wallet Application Solutions
Introduction Digital wallet applications have become a critical component of today’s digital payment ecosystem. From peer-to-peer transfers to online and in-store payments, users rely on eWallet applications to manage sensitive financial transactions securely. As adoption increases, trust has emerged as the most important factor influencing user acceptance and long-term usage.
By Nayel Basim Al Shehhi2 months ago in 01
Healthcare API Penetration Testing: A Practical Guide for Security Teams
Healthcare organizations depend on APIs to connect electronic health records, patient portals, diagnostics platforms, billing systems, and third-party healthcare services. These APIs enable real-time data exchange and operational efficiency, but they also introduce significant security risks if left untested or misconfigured.
By Sam Bishop2 months ago in 01
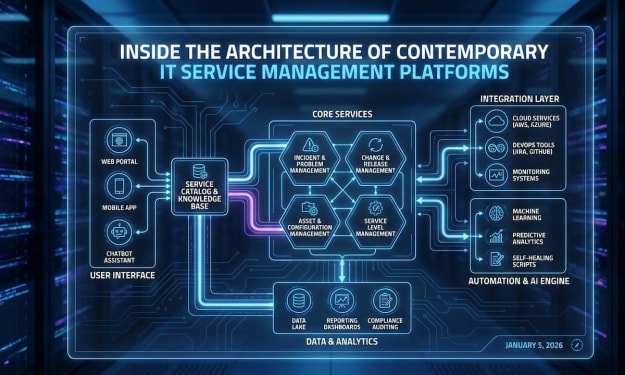
Inside the Architecture of Contemporary IT Service Management Platforms
Introduction As organizations increasingly rely on digital systems to operate efficiently, IT Service Management (ITSM) platforms have become a critical component of modern enterprises. These platforms help manage IT services, streamline workflows, and ensure consistent service delivery. Behind every effective ITSM solution lies a carefully designed architecture that integrates multiple technologies, processes, and systems.
By Nayel Basim Al Shehhi2 months ago in 01
Why Everyone Feels Burned Out in the Age of Hustle Culture
It’s 10 p.m., your laptop is still open, and you’re scrolling through work emails, social media, and half-finished projects. You tell yourself: “Just one more task.” But deep down, you know this isn’t sustainable. Welcome to the age of hustle culture — a world where being busy has become a badge of honor, and burnout is almost expected.
By Yasir khan2 months ago in 01
How Technology Is Shaping Modern Dating Applications
Introduction Dating applications have transformed how people connect and build relationships in the digital age. What started as simple profile-based platforms has evolved into sophisticated systems powered by advanced technology. Modern dating apps now focus on user experience, security, personalization, and scalability to meet growing user expectations.
By Nayel Basim Al Shehhi2 months ago in 01
What Is a Security Operations Center (SOC) and Why Businesses Are Moving to Managed SOC Services
In today’s highly connected digital world, cybersecurity is no longer just an IT concern—it is a core business priority. Organizations rely on digital systems for daily operations, customer communication, financial transactions, and data storage. As businesses grow more dependent on technology, cyber threats grow more frequent, more complex, and more damaging. This has led many organisations, especially those operating in fast-paced markets like the United Arab Emirates, to rethink how they monitor and protect their digital environments. One of the most effective approaches to modern cybersecurity is the use of a Security Operations Center, commonly known as a SOC.
By Preethu Sonu2 months ago in 01